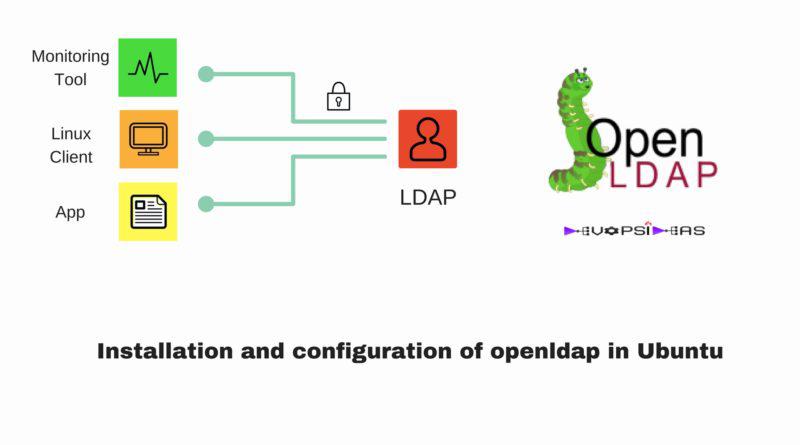
Run centralised authentication server OpenLDAP ubuntu 20
OpenLDAP is a free, open-source implementation of the Lightweight Directory Access Protocol developed by the OpenLDAP Project. It is released under its own BSD-style license called the OpenLDAP Public
Install and Setup OpenLDAP Server on Ubuntu 20.04
The OpenLDAP suite include;
- slapd – stand-alone LDAP daemon (server)
- libraries implementing the LDAP protocol, and
- utilities, tools, and sample clients
You can buy a powerful VPS (virtual private server) from Gavedu with very little cost.
Run System Update
Before you begin, ensure your system package cache is up-to-date.
apt updateapt upgrade
Want to know whether to reboot your system after upgrade? Simply install needrestart package to help you with that.
Install Stand-alone LDAP Daemon (SLAPD) on Ubuntu 20.04
To install SLAP and other LDAP utilities, run the command below;
apt install slapd ldap-utils
During the installation, you are prompted to set the OpenLDAP administrative password.
Set the password and press ENTER confirm the password set.
Configuring OpenLDAP on Ubuntu 20.04
By default, the SLAPD installer doesn’t prompt you to enter the domain information settings. It however auto-populates the the DIT with sample data based on your server domain name.
slapcatdn: dc=kifarunix-demo,dc=comobjectClass: topobjectClass: dcObjectobjectClass: organizationo: kifarunix-demo.comdc: kifarunix-demostructuralObjectClass: organizationentryUUID: 523af726-25a0-103a-8c03-87de2c08c2d4creatorsName: cn=admin,dc=kifarunix-demo,dc=comcreateTimestamp: 20200508175142ZentryCSN: 20200508175142.880878Z#000000#000#000000modifiersName: cn=admin,dc=kifarunix-demo,dc=commodifyTimestamp: 20200508175142Zdn: cn=admin,dc=kifarunix-demo,dc=comobjectClass: simpleSecurityObjectobjectClass: organizationalRolecn: admindescription: LDAP administratoruserPassword:: e1NTSEF9M1hkZ3h5SmRsK3IyclNkbkhxTzlqMXlrdS9ZWnk0Sis=structuralObjectClass: organizationalRoleentryUUID: 523b1daa-25a0-103a-8c04-87de2c08c2d4creatorsName: cn=admin,dc=kifarunix-demo,dc=comcreateTimestamp: 20200508175142ZentryCSN: 20200508175142.881901Z#000000#000#000000modifiersName: cn=admin,dc=kifarunix-demo,dc=commodifyTimestamp: 20200508175142Z
If you want to set your own DIT, you need to reconfigure SLAPD package.
dpkg-reconfigure slapd
When run, you are prompted on whether to omit the OpenLDAP server configuration. Select No and proceed to configure your OpenLDAP settings.
- Set your DNS domain name for constructing the base DN of your LDAP directory.
- Enter the name of your organization to be used in the base DN.
- Re-enter the name of your administration password and confirm it.
- Choose to remove SLAPD database when slapd package is removed.
In our example setup, the base DN is set to dc=kifarunix-demo,dc=com, root DN is set to cn=admin,dc=kifarunix-demo,dc=com.
ldapsearch -x -LLL -b "" -s base namingContextsdn:namingContexts: dc=kifarunix-demo,dc=com
To view the RootDN, run the command below
ldapsearch -H ldapi:/// -Y EXTERNAL -b "cn=config" -LLL -Q | grep olcRootDN:olcRootDN: cn=admin,dc=kifarunix-demo,dc=com
Configure OpenLDAP Logging on Ubuntu 20.04
Log files is the first place you might want to be checking in case something is not working out. By default, OpenLDAP logging level is set to none which is required to have high priority messages only logged.
ldapsearch -H ldapi:/// -Y EXTERNAL -b "cn=config" -LLL -Q | grep olcLogLevel:olcLogLevel: none
If you need to change this to a different log level, say to stats level (logs connections/operations/results), run the command below;
ldapmodify -Y EXTERNAL -H ldapi:/// -Q
The paste the content below to modify the log level.
dn: cn=configchangeType: modifyreplace: olcLogLevelolcLogLevel: stats
Next, press ENTER. Once you see a line, modifying entry "cn=config", then press Ctrl+d.
You can as well use LDIF files to update this information if you like.
To confirm the changes;
ldapsearch -Y EXTERNAL -H ldapi:/// -b cn=config "(objectClass=olcGlobal)" olcLogLevel -LLL -Qdn: cn=configolcLogLevel: stats
Next, you need to specify the log file for OpenLDAP on Rsyslog configuration. By default, OpenLDAP logs to local4 facility, hence, to configure it to log to /var/log/slapd.log for example, execute the command below;
echo "local4.* /var/log/slapd.log" >> /etc/rsyslog.d/51-slapd.conf
Restart Rsyslog and SLAPD service
systemctl restart rsyslog slapd
You should now be able to read the LDAP logs on, /var/log/slapd.log.
You can as well configure log rotation;
vim /etc/logrotate.d/slapd/var/log/slapd.log{rotate 7dailymissingoknotifemptydelaycompresscompresspostrotate/usr/lib/rsyslog/rsyslog-rotateendscript}
Restart log rotation service;
systemctl restart logrotate
Configure LDAP with SSL/TLS Certificates
LDAP supports two methods to encrypt communications using SSL/TLS:
LDAPS: LDAPS communication usually occurs over a special port, commonly 636.STARTTLS: STARTTLS connections begin as a plaintext over the standard LDAP port (389), and that connection is then upgraded to SSL/TLS. It is also known as TLS upgrade operation.
In this demo, we are using self-signed certificates. Follow the link below to configure OpenLDAP server with SSL/TLS certificates.
How to Configure OpenLDAP server with Signed SSL/TLS certificates
If while updating the TLS certificates you get the error below;
modifying entry "cn=config"ldap_modify: Other (e.g., implementation specific) error (80)
And checking the syslog files, you find AppArmor denying read access to the the certificate and key files;
May 9 12:54:08 ldap kernel: [ 3785.915065] audit: type=1400 audit(1589028848.345:137): apparmor="DENIED" operation="open" profile="/usr/sbin/slapd" name="/etc/ssl/openldap/certs/cacert.pem" pid=5141 comm="slapd" requested_mask="r" denied_mask="r" fsuid=112 ouid=112
You need to update the AppArmor to give slapd read access to the certificates and key files by editing the SLAPD AppArmor profile and adding the lines below;
vim /etc/apparmor.d/usr.sbin.slapd...# Site-specific additions and overrides. See local/README for details.#include#TLS/etc/ssl/openldap/certs/ r,/etc/ssl/openldap/certs/* r,/etc/ssl/openldap/private/ r,/etc/ssl/openldap/private/* r,}
Replace the paths to certificate files and keys accordingly. Save and exit the file and reload SLAPD AppArmor profile;
apparmor_parser -r /etc/apparmor.d/usr.sbin.slapd
Note, if you are using standard certificate and keys path, then the AppArmor changes might not be necessary.
Once that is done, retry to update SLAPD database with TLS certificates.
To verify that the files are in place;
slapcat -b "cn=config" | grep "olcTLS"olcTLSCACertificateFile: /etc/ssl/openldap/certs/cacert.pemolcTLSCertificateFile: /etc/ssl/openldap/certs/ldapserver-cert.crtolcTLSCertificateKeyFile: /etc/ssl/openldap/private/ldapserver-key.key
Next, update the path to CA certificate file on /etc/ldap/ldap.conf.
sed -i 's|certs/ca-certificates.crt|openldap/certs/cacert.pem|' /etc/ldap/ldap.conf
Configure OpenLDAP to Provide SUDO Access for Users
To enable OpenLDAP to provide sudo access for users, proceed as follows;
Install OpenLDAP sudo package;
export SUDO_FORCE_REMOVE=yesapt install sudo-ldap
Create OpenLDAP SUDO schema;
Copy the sample OpenLDAP sudo schema to OpenLDAP schemas directory
cp /usr/share/doc/sudo-ldap/schema.OpenLDAP /etc/ldap/schema/sudo.schema
Configure OpenLDAP to include SUDO schema in its database.
For this, we will create a temporary directory from where we will convert the sudo schema to LDIF before we can configure SLAPD to include it in its database.
mkdir /tmp/ldap-sudoecho "include /etc/ldap/schema/sudo.schema" > /tmp/ldap-sudo/ldapsudo.confcd /tmp/ldap-sudo
Generate SUDO LDIF file from the schema;
slaptest -f ldapsudo.conf -F .config file testing succeeded
The sudo LDIF file should now be located under the cn\=config/cn\=schema/
ls cn\=config/cn\=schema/'cn={0}sudo.ldif'
Edit the LDAP SUDO LDIF file and REMOVE comment lines (Lines beginning with #) at the top and update the lines;
dn: cn={0}sudoobjectClass: olcSchemaConfigcn: {0}sudo
such that they look like;
dn: cn=sudo,cn=schema,cn=configobjectClass: olcSchemaConfigcn: sudo
Also, REMOVE these lines at the bottom;
structuralObjectClass: olcSchemaConfigentryUUID: a0db89da-2646-103a-83d7-df36427f181ecreatorsName: cn=configcreateTimestamp: 20200509134211ZentryCSN: 20200509134211.249833Z#000000#000#000000modifiersName: cn=configmodifyTimestamp: 20200509134211Z
Once done editing the sudo LDIF file, update the SLAPD database to include SUDO schema;
ldapadd -Q -Y EXTERNAL -H ldapi:/// -f 'cn=config/cn=schema/cn={0}sudo.ldif'
You should see a line;
adding new entry "cn=sudo,cn=schema,cn=config"
Enable sudo user and host indexing;
ldapadd -Y EXTERNAL -H ldapi:/// -Q
When the command runs, paste te content below and press ENTER.
dn: olcDatabase={1}mdb,cn=configchangetype: modifyadd: olcDbIndexolcDbIndex: sudoUser,sudoHost pres,eq
Once you see the line, modifying entry "olcDatabase={1}mdb,cn=config", press ctrl+d.
To verify indexing;
slapcat -n 0 | grep olcDbIndexolcDbIndex: objectClass eqolcDbIndex: cn,uid eqolcDbIndex: uidNumber,gidNumber eqolcDbIndex: member,memberUid eqolcDbIndex: sudoUser,sudoHost pres,eq
Your OpenLDAP should now be able to provide SUDO access for users. This is subject to further configuration, however. Follow the link below to complete on this;
How to Configure SUDO access via OpenLDAP Server
Create OpenLDAP User Accounts
Before we can create OpenLDAP user accounts, we need to create the organization unit containers for storing users and their group information. See our example below. Be sure to make the relevant changes as per your environment setup.
vim users-ou.ldifdn: ou=people,dc=kifarunix-demo,dc=comobjectClass: organizationalUnitobjectClass: topou: peopledn: ou=groups,dc=kifarunix-demo,dc=comobjectClass: organizationalUnitobjectClass: topou: groups
Before you can be able to update the database with the users OU information above, you need to adjust the SLAPD database access controls;
vim update-mdb-acl.ldifdn: olcDatabase={1}mdb,cn=configchangetype: modifyreplace: olcAccessolcAccess: to attrs=userPassword,shadowLastChange,shadowExpireby self writeby anonymous authby dn.subtree="gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth" manageby dn.exact="cn=readonly,ou=people,dc=kifarunix-demo,dc=com" readby * noneolcAccess: to dn.exact="cn=readonly,ou=people,dc=kifarunix-demo,dc=com" by dn.subtree="gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth" manage by * noneolcAccess: to dn.subtree="dc=kifarunix-demo,dc=com" by dn.subtree="gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth" manageby users readby * none
Save and exit the file.
Note that we have included the access controls for the Read Only Bind DN user that we will create later in this guide.
Update database ACL with the above information by running the command below;
ldapadd -Y EXTERNAL -H ldapi:/// -f update-mdb-acl.ldif
Once that is done, you should now be able, as the admin, to create the users OU as shown above. Therefore, to update the database with the user OU information above, run the command below;
ldapadd -Y EXTERNAL -H ldapi:/// -f users-ou.ldif...adding new entry "ou=people,dc=kifarunix-demo,dc=com"adding new entry "ou=groups,dc=kifarunix-demo,dc=com"
Once you have the user OU containers created, you can now add user accounts. In this demo, we will create a user called johndoe in our OpenLDAP database.
vim johndoe.ldifdn: uid=johndoe,ou=people,dc=kifarunix-demo,dc=comobjectClass: inetOrgPersonobjectClass: posixAccountobjectClass: shadowAccountuid: johndoecn: Johnsn: DoeloginShell: /bin/bashuidNumber: 10000gidNumber: 10000homeDirectory: /home/johndoeshadowMax: 60shadowMin: 1shadowWarning: 7shadowInactive: 7shadowLastChange: 0dn: cn=johndoe,ou=groups,dc=kifarunix-demo,dc=comobjectClass: posixGroupcn: johndoegidNumber: 10000memberUid: johndoe
To add the user johndoe to the database using the information above, run the command below;
ldapadd -Y EXTERNAL -H ldapi:/// -f johndoe.ldifadding new entry "uid=johndoe,ou=people,dc=kifarunix-demo,dc=com"adding new entry "cn=johndoe,ou=groups,dc=kifarunix-demo,dc=com"
Setting Password for LDAP User
If you noticed, in the above, we didn’t set any password for the user. To set/reset the password for the user, run the command below;
ldappasswd -H ldapi:/// -Y EXTERNAL -S "uid=johndoe,ou=people,dc=kifarunix-demo,dc=com"
To verify user’s password;
ldapwhoami -h ldap.kifarunix-demo.com -x -D "uid=johndoe,ou=people,dc=kifarunix-demo,dc=com" -W
If the password is correct, you should see the user’s DN;
dn:uid=johndoe,ou=people,dc=kifarunix-demo,dc=com
Create OpenLDAP BIND DN
There are two OpenLDAP BIND DNs;
Administrator Bind DN: defines admin username and password. It is used only for querying the directory server and so this user must have privileges to search the directory.User Bind DN: defines the user username and password is used for authentication and password change operations.
In this demo, we will create a user Bind DN called readonly for read operations.
Generate the password hash for the bind DN user;
slappasswdNew password: passwordRe-enter new password: password{SSHA}qUwFrgsseX1ztrJ64wq63SNqGuSnLics
Copy the hash above and replace it with the value of userPassword below;
vim readonly-user.ldifdn: cn=readonly,ou=people,dc=kifarunix-demo,dc=comobjectClass: organizationalRoleobjectClass: simpleSecurityObjectcn: readonlyuserPassword: {SSHA}qUwFrgsseX1ztrJ64wq63SNqGuSnLicsdescription: Bind DN user for LDAP Operations
Add the bind user to the LDAP database;
ldapadd -Y EXTERNAL -H ldapi:/// -f readonly-user.ldifadding new entry "cn=readonly,ou=people,dc=kifarunix-demo,dc=com"
Define the access controls for the user bind DN. See what we have in our ACL file above. Or simply run the command below to check the ACLs defined;
ldapsearch -Q -LLL -Y EXTERNAL -H ldapi:/// -b cn=config '(olcDatabase={1}mdb)' olcAccess
Allow OpenLDAP Service on Firewall
If UFW is running, allow OpenLDAP (both LDAP and LDAPS) external access;
ufw allow "OpenLDAP LDAP"ufw allow "OpenLDAP LDAPS"
Authenticate Via OpenLDAP Server
The basic installation and configuration of OpenLDAP server on Ubuntu 20.04 is done. All you can do now is to configure your clients to authenticate via OpenLDAP;
Follow the link below to learn how to configure SSSD for OpenLDAP authentication on Ubuntu 20.04;
Gopal Jani
https://www.linkedin.com/in/gopal-jani/







No comments yet. Login to start a new discussion Start a new discussion